Search results for tag #dnssec
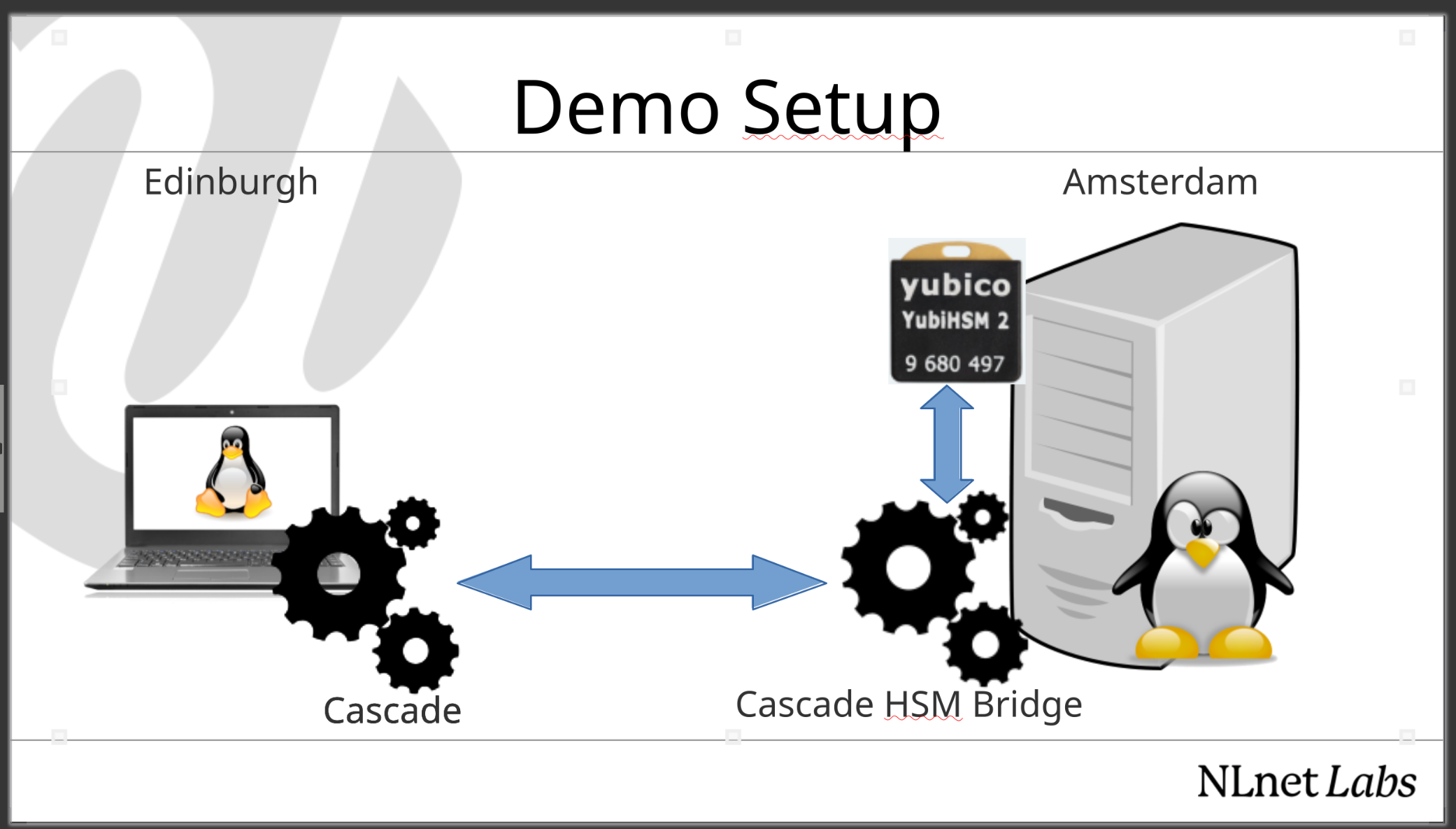
@ximon18 @dnsoarc after his talk on stage, Ximon will be at the demo table in the lunch area, where he can show all the other tricks Cascade has learned since OARC 45 in Stockholm.
Also, make sure to bring your zone files so you can for example see how fast parallel #Dnssec signing by @bal4e really is. #DNS #LoveDNS #OpenSource
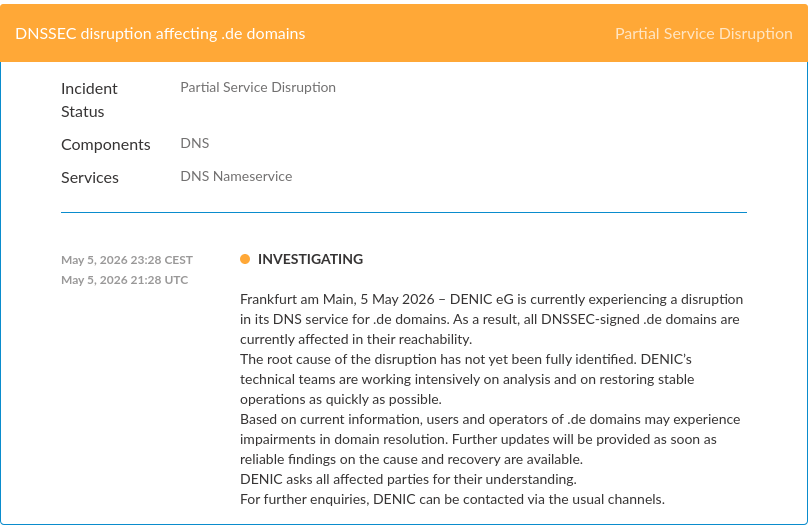
DENIC: “Analysis of the DNS outage on 5 May 2026”
English: https://blog.denic.de/en/analysis-of-the-dns-outage-on-5-may-2026/
German: https://blog.denic.de/analyse-des-dns-ausfalls-vom-5-mai-2026/
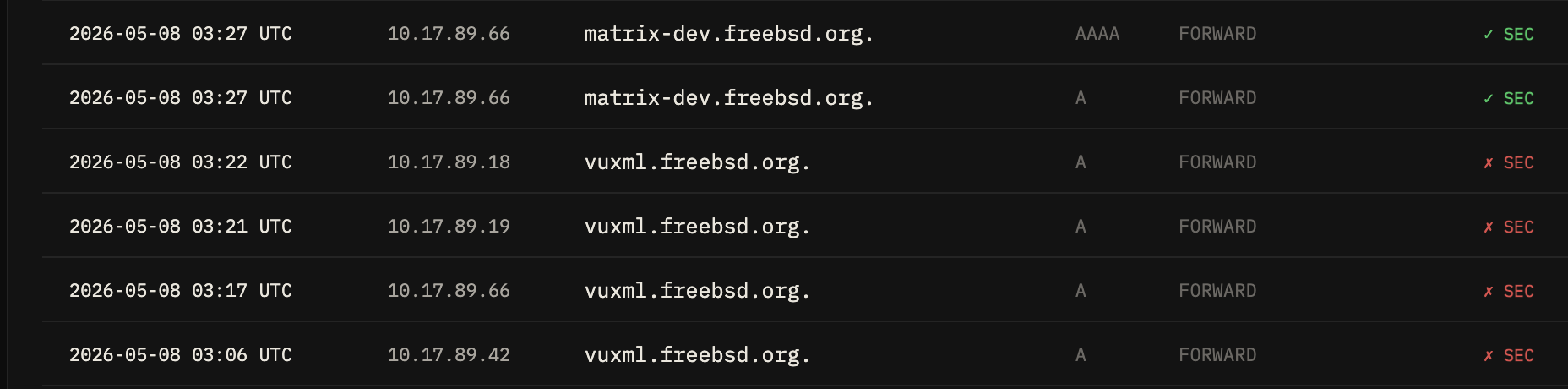
Quad1 and Quad9 appear to have added an NTA (negative trust anchor) for .DE which means validators will no longer validate domains below *.DE; the situation will thus resolve (pun not really intended) itself soon’ish if temporarily until the root cause is fixed and the NTAs are removed.
Quad8 is still validating .DE
Here is Quad9’s NTA: https://quad9.net/api/ntas.txt
Am I the only one having #DNSSEC problems with #DENIC?
Unbound is throwing me a lot of DNSSEC bogus on some .de domains 🤔
$ dig welt.de
...
;; ->>HEADER<<- opcode: QUERY, status: SERVFAIL, id: 21366
...
; EDE: 6 (DNSSEC Bogus): (validation failure <welt.de. A IN>: signature crypto failed from 2a02:568:0:2::53 for DS welt.de. while building chain of trust)
Edit: issue seems fixed.
Looks like DE ccTLD is unresolvable due to DNSSEC issue:
https://dnsviz.net/d/nic.de/afpsNg/dnssec/
😬
🧵👇
RE: https://mastodon.social/@jpmens/116522310229612501
IANA has a chance to do the funniest thing ever… 
John Shaft boostedRolling the root #DNSSEC key:
"The next KSK key roll is underway as of May 2026. This is not a change of algorithm, but simply a change of the private key value. The incoming KSK (KSK-2024) was published on the IANA website in July 2024 and added to the root zone’s DNSKEY Resource Record in January 2025. The IANA plans to roll the KSK in October 2026, when it will be used for generating the root zone’s DNSKEY Resource Record digital signatures"
Rolling the root #DNSSEC key:
"The next KSK key roll is underway as of May 2026. This is not a change of algorithm, but simply a change of the private key value. The incoming KSK (KSK-2024) was published on the IANA website in July 2024 and added to the root zone’s DNSKEY Resource Record in January 2025. The IANA plans to roll the KSK in October 2026, when it will be used for generating the root zone’s DNSKEY Resource Record digital signatures"
@bortzmeyer après plusieurs timeout
Mais je suis en forêt avec un téléphone
C'est pas idéal pour déboguer :-) surtout #dnssec sur lequel je suis nul
PowerDNS DNSdist 1.9.14 and 2.0.5 Released
https://blog.powerdns.com/2026/04/23/powerdns-dnsdist-1.9.14-and-2.0.5-released
PowerDNS Security Advisory 2026-05 for PowerDNS Authoritative Server
(aka PowerDNS Authoritative Server 4.9.14 and 5.0.4 released)
PowerDNS Security Advisory 2026-03 for PowerDNS Recursor
(aka PowerDNS Recursor 5.2.9, 5.3.6 and 5.4.1 released)
https://blog.powerdns.com/2026/04/22/powerdns-security-advisory-2026-03
PowerDNS Security Advisory 2026-04 for PowerDNS DNSdist
(aka DNSdist 1.9.13 and 2.0.4 released)
https://blog.powerdns.com/2026/04/22/powerdns-security-advisory-2026-04-for-powerdns-dnsdist
PowerDNS DNSdist 1.9.12 and 2.0.3 Released (Security Release)
https://blog.powerdns.com/2026/03/31/powerdns-dnsdist-1.9.12-and-2.0.3-released
We're thrilled that Cascade is among the first projects supported by the Nominet DNS Fund.
With Nominet's support, our new DNSSEC signing solution receives a massive push forward, allowing our team to focus on implementing speed improvements, a reduced memory footprint and essentials such as incremental signing.
We'll be launching a beta in April, followed by an initial production release in June 2026.
So, previously on post-quantum #DNSSEC: not a lot of action. Standardized post-quantum cryptography algorithms like ML-DSA have keys and signatures which are way too long for the #DNS.
https://mastodon.gougere.fr/@DNSresolver/116241567126448201
TLS can deal with it (they run on TCP or QUIC) but we cannot, with UDP. No obvious solution.
PowerDNS Recursor 5.4.0 Released
https://blog.powerdns.com/2026/03/09/powerdns-recursor-5.4.0-released
With memory prices skyrocketing we're happy to bring you some good news on the #DNS front.
In version 4.14.0 of our authoritative nameserver NSD we vastly reduced the memory footprint by refactoring the RDATA storage, with gains up to 50%.
Overall, relatively large #DNSSEC-signed zones like .nl and .se benefit the most, but being able to bring the memory requirements to serve .com below 64GB is pretty awesome too.
We're eager to hear the improvements you're seeing!